top of page
The Invisible Link: Inside the PE Header's Connection to PDBs
Have you ever loaded an executable into WinDbg or Visual Studio and watched as it instantly found the matching symbols? It lights up the call stack with function names and snaps right to the source code line. It feels seamless, but underneath that convenience lies a rigid, decades-old structure embedded in every Windows EXE and DLL. The binary itself holds the map to its own debugging information. Whether you are into reverse engineering, malware analysis, or just optimizing

Josh Stroschein
Nov 23, 20255 min read


Analyzing Shellcode with SCLauncher
Analyzing and debugging shellcode is a common task when performing malware analysis, exploit development and reverse engineering....

Josh Stroschein
Mar 18, 20244 min read


Customizing FakeNet-NG's Default Web Root
This article delves into tailoring Fakenet-NG 's default web root, empowering you to craft a more precise and controlled environment for...

Josh Stroschein
Mar 4, 20242 min read


Identifying UserForms with Oledump and Olevba
Malware authors often find creative ways to obfuscate and store their data and malicious office documents are no exception. One such...

Josh Stroschein
Feb 28, 20242 min read


OneNote Malware: Hidden Payloads in Page Versions
While the abuse of OneNote documents is nothing new, a recent document I investigated revealed multiple payloads through the page...

Josh Stroschein
Feb 16, 20242 min read


Anti-Analysis in JavaScript Executed by Windows Script Host (WSH)
Note: This blog was originally published on Feb 24, 2020 It’s common to see malicious office documents drop a JavaScript (JS) file to be...

Josh Stroschein
Feb 11, 20242 min read
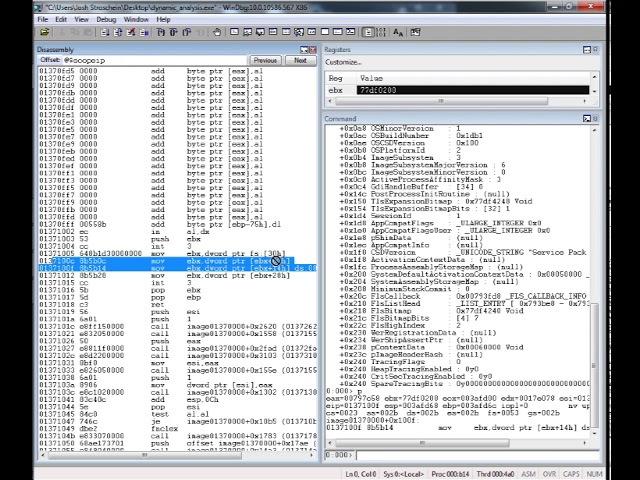
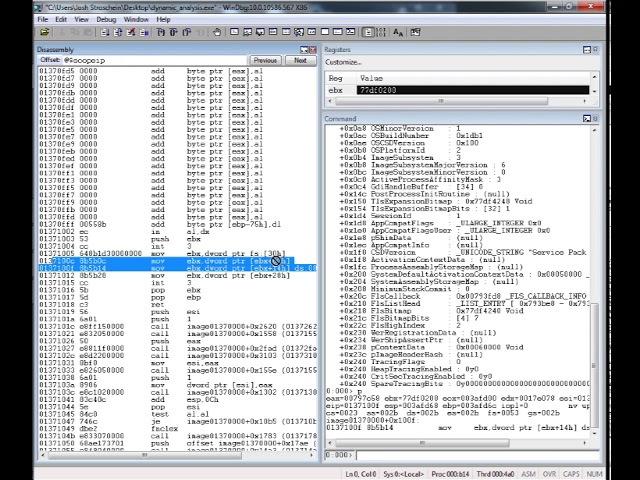
Locating DLL Name from the Process Environment Block (PEB)
I often encounter software, especially when performing malware analysis, that dynamically constructs it’s own import table. This can be...

Josh Stroschein
Feb 10, 20245 min read
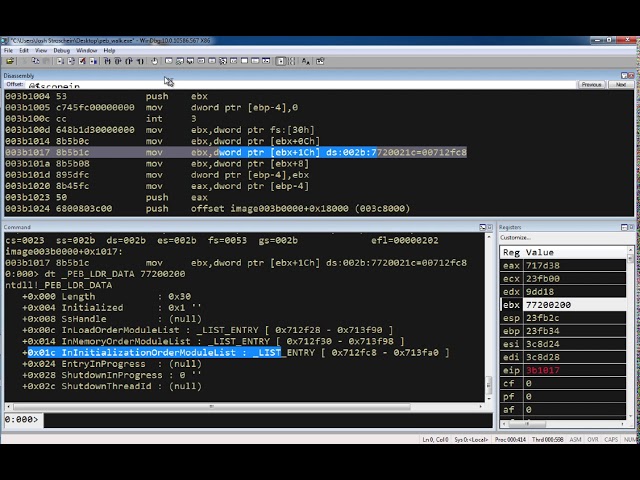
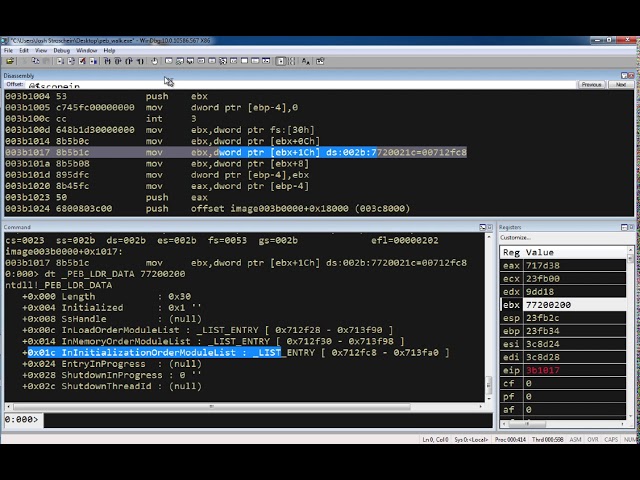
Exploring the Process Environment Block (PEB) with WinDbg
The source code for this example can be found here. The assembly is: mov ebx, fs:[ 0x30 ] ; // get a pointer to the PEB mov ebx, [ ebx +...

Josh Stroschein
Feb 10, 20241 min read


Maldoc Uses Template Injection for Macro Execution
Note - this was originally published in May of 2020 I recently came across a handful of malicious office documents (maldocs) whose...

Josh Stroschein
Feb 8, 20242 min read


How-To: Installing Oledump in Windows
In this video, we’ll look into installing OLEDUMP in Microsoft Windows. Microsoft office documents are a common vehicle used by malware...

Josh Stroschein
Feb 11, 20211 min read


Creating an IDA Python Plugin for Static XOR String Deobfuscation
In this video, we’ll explore a recent XLS document that drops and executes a DLL using RUNDLL32. The DLL is small and only used to...

Josh Stroschein
Jan 6, 20211 min read


Emotet Maldoc Analysis – Embedded DLL and CertUtil for Base64 Decoding
On 11/10/2020, AnyRun posted an Emotet maldoc that utilized CertUtil to decode a DLL payload that was used for unpacking and running the...

Josh Stroschein
Dec 2, 20201 min read
Excel 4 Macros – Get.Workspace Reference
With the recent resurgence of the use of Excel 4 macros in malicious excel documents, I’ve found myself scouring the internet looking for...

Josh Stroschein
Apr 12, 20201 min read


Removing Passwords from VBA Projects
Occasionally I’ll encounter a maldoc that has a password-protected VBA project. While tools such as oledump may still extract the macros,...

Josh Stroschein
Apr 9, 20202 min read


Maldoc drops DLL and executes via ExecuteExcel4Macro
Behavioral information is a key indicator used to determine if an office document is malicious or not. I’ve recently seen a series of...

Josh Stroschein
Mar 25, 20203 min read


Maldoc uses Windows API to perform process hollowing
A favorite technique by malware authors is to use macros in their office documents to utilize a normal system executable and replace the...

Josh Stroschein
Mar 18, 20205 min read


Maldoc uses RC4 to hide PowerShell script, retrieves payload from DNS TXT record
Malware authors are constantly coming up with new and clever techniques to help avoid detection. In this maldoc, the authors employed...

Josh Stroschein
Mar 10, 20203 min read
Disabling Teredo IPv6 Tunnelling
If you’re seeing DNS queries for teredo.ipv6.microsoft.com you may be interested in disabling it (more at MSDN and WikiPedia). On Windows...

Josh Stroschein
Feb 29, 20201 min read


Malware Analysis – Triaging Emotet (Fall 2019)
This is a summary of initial (triage) analysis of Emotet droppers and the associated network traffic from the fall of 2019. This write-up...

Josh Stroschein
Feb 10, 20205 min read


How to Disable Microsoft Error Reporting
If you’ve ever encountered the following dialog – you know that an application has crashed in Windows. As the dialog indicates, Microsoft...

Josh Stroschein
Jan 26, 20201 min read
bottom of page