top of page


Identifying UserForms with Oledump and Olevba
Malware authors often find creative ways to obfuscate and store their data and malicious office documents are no exception. One such...

Josh Stroschein
Feb 28, 20242 min read


OneNote Malware: Hidden Payloads in Page Versions
While the abuse of OneNote documents is nothing new, a recent document I investigated revealed multiple payloads through the page...

Josh Stroschein
Feb 16, 20242 min read


Anti-Analysis in JavaScript Executed by Windows Script Host (WSH)
Note: This blog was originally published on Feb 24, 2020 It’s common to see malicious office documents drop a JavaScript (JS) file to be...

Josh Stroschein
Feb 11, 20242 min read
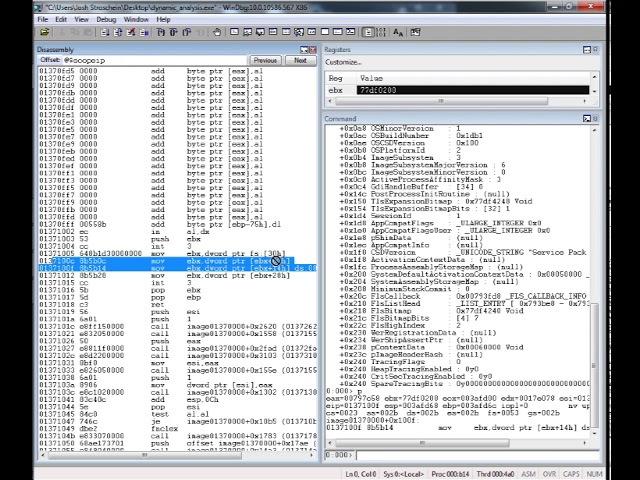
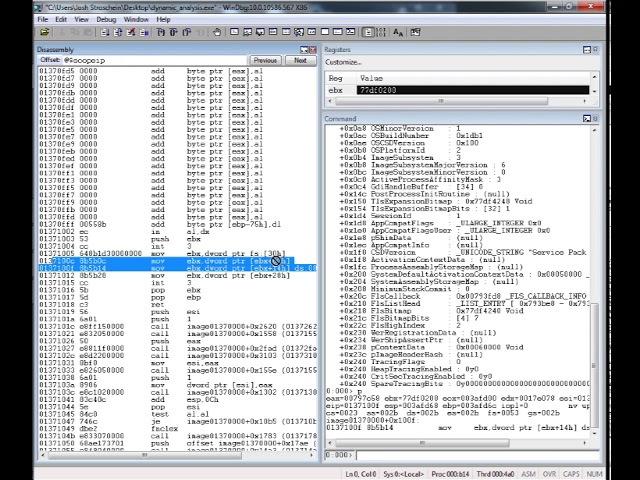
Locating DLL Name from the Process Environment Block (PEB)
I often encounter software, especially when performing malware analysis, that dynamically constructs it’s own import table. This can be...

Josh Stroschein
Feb 10, 20245 min read
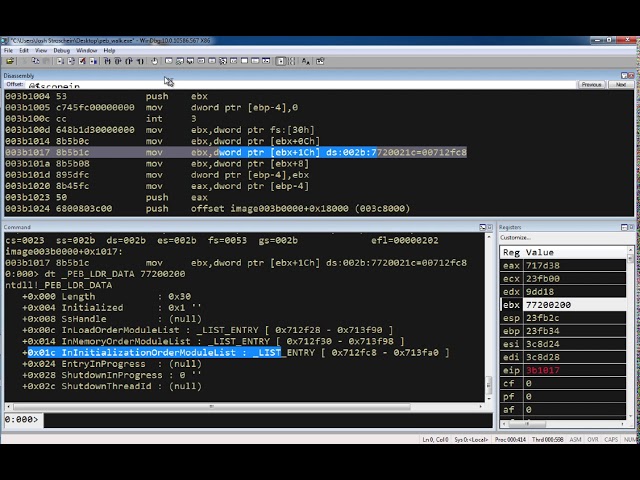
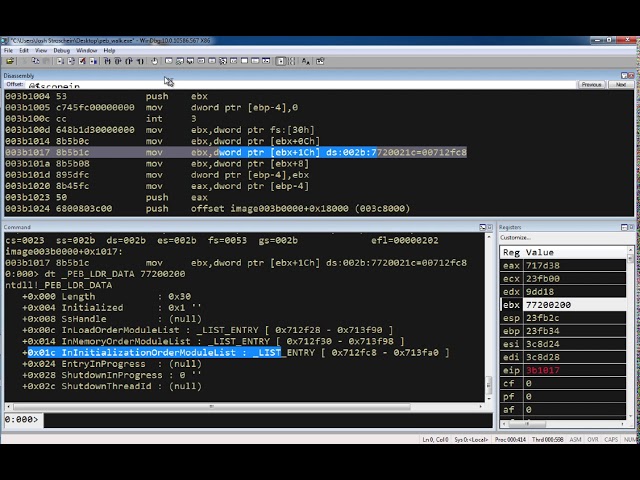
Exploring the Process Environment Block (PEB) with WinDbg
The source code for this example can be found here. The assembly is: mov ebx, fs:[ 0x30 ] ; // get a pointer to the PEB mov ebx, [ ebx +...

Josh Stroschein
Feb 10, 20241 min read


Maldoc Uses Template Injection for Macro Execution
Note - this was originally published in May of 2020 I recently came across a handful of malicious office documents (maldocs) whose...

Josh Stroschein
Feb 8, 20242 min read
bottom of page